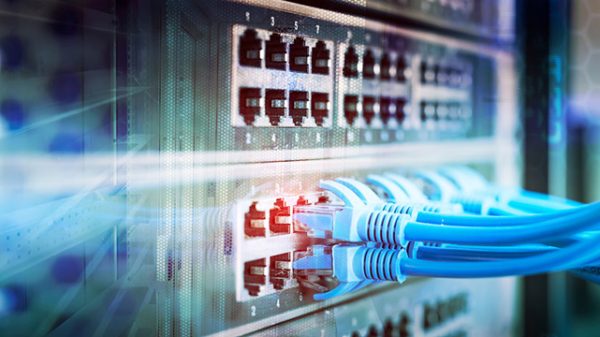
The Internet of Things (IoT for short) is the collective reference for a network of interconnected devices that work to communicate and exchange data with one another across the Internet. It is not an understatement to say that the rapid advancement of IoT has completely revolutionized many aspects of life, from wearable devices to smart homes to healthcare to industrial automation and more, affecting both commercial and personal activity.
With this surge in connectivity comes an accompanying escalation of cyber threats including spear phishing, ransomware, and more personal online blackmail and sextortion. To combat these threats, it is vital to understand them in detail, which leads to a greater understanding of how to prevent and respond to them with the help of advanced digital forensics.
Understanding IoT-Specific Threats
Device Vulnerabilities
IoT devices will very often possess limited memory and processing power, which leads to an inadequacy of security features. This makes such devices an easy target for hackers who can attack weak passwords and outdated firmware. Once they are compromised, your devices can be used to collect large amounts of sensitive information.
Lack Of Standardization
The IoT ecosystem encapsulates a wide range of devices from a wide range of manufacturers, each with its own sets and standards of security protocols. Because of this lack of standardization across the spectrum, a number of inconsistencies in security measures will be present that attackers can work to exploit.
Data Privacy Concerns
IoT devices inherently collect and transmit large amounts of data, which can be personal and sensitive, especially in the case of consumer IoT or smart home devices. If any of this data gets intercepted by unauthorized parties, it can be used for purposes like sextortion or blackmail. This can be common in the realms of wearable health devices and smart cameras.
Network Security Gaps
IoT devices are usually connected to much larger networks, and the fact is that even a single compromised device within a network can provide access for attackers to perform a much wider infiltration.
Prevention Measures
So, what can be done to mitigate the above-listed risks that are so heavily associated with IoT devices? Several steps can be taken to best protect a device/network.
Strengthen Device Security
The first thing to do is make sure that all of your IoT devices are regularly updated to their latest firmware versions including any relevant security patches. Manufacturers are diligent in providing timely updates, but these can only be effective if users apply them as soon as they become available. In addition, creating stronger, more unique passwords for devices, as well as multi-factor authentication, is always a recommended step. Always avoid default, ‘easy’ passwords.
Implement Enhanced Network Security
It can be immensely helpful to segregate IoT devices from critical networks, using network segmentation protocols. Doing this can limit the potential impact of a single compromised device and save lots of sensitive information from being accessed.
Implement Comprehensive Monitoring
The use of intrusion detection and prevention systems (known as IDPS) to continuously monitor an IoT network for unusual activity is highly recommended. The sooner an anomaly is detected, the more prompt a response can be and the less potential damage can be done.
Introduce Robust Data Privacy Measures
Savvy users can adopt a practice of data minimization by only collecting the most necessary amounts of data and avoiding the unnecessary storing of sensitive information on IoT devices. Going through a device’s access controls to tailor preferences and commands can ensure that all data stored on IoT devices is protected and encrypted, making it much more difficult for that data to be misused in the event of an attack.
The post The Intersection of IoT and Cybersecurity: Preventing Blackmail and Sextortion appeared first on IoT Business News.